利用Appche2,实现V2ray的WebSocket+TLS+Web伪装
所以我为什么不用Nginx呢?
从最开始倒腾vps已经一年多了,一开始只是为了科学上网,然后开始尝试自建blog,运行mc服务器之类的,其实还挺有意思的。
这段时间里换了不少服务商,国内网络环境真的太差了,即使是效果最好的GCP,晚高峰一定会掉包甚至直接断流,拿来看看网页啥的是够了,但是玩游戏特别难受。最近实在忍无可忍了,搞个CN2线路的服务器试试看,正好弄个V2ray的WebSocket+TLS+Web伪装。
虽说具体操作在V2ray的白话文教程里有,但是实际操作的时候碰上好几个问题,教程里根本没提,记录一下省得以后再走弯路。
用acme.sh签发证书
在第一次用了acme.sh过后,我就再也没用过别的方法自己签发ssl证书了,真的好用。
安装acme.sh和创建证书都没啥问题,安装证书的命令有点麻烦。
acme.sh --install-cert -d stsecurity.moe --cert-file /etc/apache2/ssl/cert.cer --key-file /etc/apache2/ssl/key.key --fullchain-file /etc/apache2/ssl/fullchain.cer --ca-file /etc/apache2/ssl/ca.cer --reloadcmd "service apache2 force-reload"之前每次都复制主页上的代码一点点改,太麻烦了,这段只需要改个域名就行了。
配置V2ray服务端
服务端基本上按着教程来就行了,就是path得跟后面保持一致,教程里appche的配置里path是/ray/。
{
"inbounds": [
{
"port": 10000,
"listen":"127.0.0.1",//只监听 127.0.0.1,避免除本机外的机器探测到开放了 10000 端口
"protocol": "vmess",
"settings": {
"clients": [
{
"id": "b831381d-6324-4d53-ad4f-8cda48b30811",
"alterId": 64
}
]
},
"streamSettings": {
"network": "ws",
"wsSettings": {
"path": "/ray/"
}
}
}
],
"outbounds": [
{
"protocol": "freedom",
"settings": {}
}
]
}配置Appche
这里我搞了好久一直报错,重复了好多次,只要加上
<Location "/ray/">
ProxyPass ws://127.0.0.1:10000/ray/ upgrade=WebSocket
ProxyAddHeaders Off
ProxyPreserveHost On
RequestHeader append X-Forwarded-For %{REMOTE_ADDR}s
</Location>就启动不了Appche,后来找到一篇文章《WebSocket+TLS+CDN+Web,Apache2 部署V2Ray》,发现是没启用Appche的一些模组。
所以首先启用模组:
sudo a2enmod ssl
sudo a2enmod proxy
sudo a2enmod proxy_wstunnel
sudo a2enmod proxy_http
sudo a2enmod rewrite
sudo a2enmod headers然后在site-enabled文件夹中创建default-ssl.conf的快捷方式:
sudo ln -s /etc/apache2/sites-available/default-ssl.conf /etc/apache2/sites-enabled/000-default-ssl.conf之后编辑default-ssl.conf,我就在原本的基础上改了一下。
<IfModule mod_ssl.c>
<VirtualHost _default_:443>
ServerAdmin webmaster@localhost
ServerName v.stsecurity.moe
DocumentRoot /var/www/html
# Available loglevels: trace8, ..., trace1, debug, info, notice, warn,
# error, crit, alert, emerg.
# It is also possible to configure the loglevel for particular
# modules, e.g.
#LogLevel info ssl:warn
ErrorLog ${APACHE_LOG_DIR}/error.log
CustomLog ${APACHE_LOG_DIR}/access.log combined
# For most configuration files from conf-available/, which are
# enabled or disabled at a global level, it is possible to
# include a line for only one particular virtual host. For example the
# following line enables the CGI configuration for this host only
# after it has been globally disabled with "a2disconf".
#Include conf-available/serve-cgi-bin.conf
# SSL Engine Switch:
# Enable/Disable SSL for this virtual host.
SSLEngine on
# A self-signed (snakeoil) certificate can be created by installing
# the ssl-cert package. See
# /usr/share/doc/apache2/README.Debian.gz for more info.
# If both key and certificate are stored in the same file, only the
# SSLCertificateFile directive is needed.
SSLCertificateFile /etc/apache2/ssl/cert.pem
SSLCertificateKeyFile /etc/apache2/ssl/key.pem
# Server Certificate Chain:
# Point SSLCertificateChainFile at a file containing the
# concatenation of PEM encoded CA certificates which form the
# certificate chain for the server certificate. Alternatively
# the referenced file can be the same as SSLCertificateFile
# when the CA certificates are directly appended to the server
# certificate for convinience.
#SSLCertificateChainFile /etc/apache2/ssl/fullchain.pem
# Certificate Authority (CA):
# Set the CA certificate verification path where to find CA
# certificates for client authentication or alternatively one
# huge file containing all of them (file must be PEM encoded)
# Note: Inside SSLCACertificatePath you need hash symlinks
# to point to the certificate files. Use the provided
# Makefile to update the hash symlinks after changes.
#SSLCACertificatePath /etc/ssl/certs/
#SSLCACertificateFile /etc/apache2/ssl.crt/ca-bundle.crt
# Certificate Revocation Lists (CRL):
# Set the CA revocation path where to find CA CRLs for client
# authentication or alternatively one huge file containing all
# of them (file must be PEM encoded)
# Note: Inside SSLCARevocationPath you need hash symlinks
# to point to the certificate files. Use the provided
# Makefile to update the hash symlinks after changes.
#SSLCARevocationPath /etc/apache2/ssl.crl/
#SSLCARevocationFile /etc/apache2/ssl.crl/ca-bundle.crl
# Client Authentication (Type):
# Client certificate verification type and depth. Types are
# none, optional, require and optional_no_ca. Depth is a
# number which specifies how deeply to verify the certificate
# issuer chain before deciding the certificate is not valid.
#SSLVerifyClient require
#SSLVerifyDepth 10
# SSL Engine Options:
# Set various options for the SSL engine.
# o FakeBasicAuth:
# Translate the client X.509 into a Basic Authorisation. This means that
# the standard Auth/DBMAuth methods can be used for access control. The
# user name is the `one line' version of the client's X.509 certificate.
# Note that no password is obtained from the user. Every entry in the user
# file needs this password: `xxj31ZMTZzkVA'.
# o ExportCertData:
# This exports two additional environment variables: SSL_CLIENT_CERT and
# SSL_SERVER_CERT. These contain the PEM-encoded certificates of the
# server (always existing) and the client (only existing when client
# authentication is used). This can be used to import the certificates
# into CGI scripts.
# o StdEnvVars:
# This exports the standard SSL/TLS related `SSL_*' environment variables.
# Per default this exportation is switched off for performance reasons,
# because the extraction step is an expensive operation and is usually
# useless for serving static content. So one usually enables the
# exportation for CGI and SSI requests only.
# o OptRenegotiate:
# This enables optimized SSL connection renegotiation handling when SSL
# directives are used in per-directory context.
#SSLOptions +FakeBasicAuth +ExportCertData +StrictRequire
<FilesMatch "\.(cgi|shtml|phtml|php)$">
SSLOptions +StdEnvVars
</FilesMatch>
<Directory /usr/lib/cgi-bin>
SSLOptions +StdEnvVars
</Directory>
SSLProtocol -All +TLSv1 +TLSv1.1 +TLSv1.2
SSLCipherSuite HIGH:!aNULL
<LocationMatch "/ray/">
ProxyPass ws://127.0.0.1:10052/ray/ upgrade=WebSocket
ProxyAddHeaders Off
ProxyPreserveHost On
RequestHeader set Host %{HTTP_HOST}s
RequestHeader set X-Forwarded-For %{REMOTE_ADDR}s
</LocationMatch>
# SSL Protocol Adjustments:
# The safe and default but still SSL/TLS standard compliant shutdown
# approach is that mod_ssl sends the close notify alert but doesn't wait for
# the close notify alert from client. When you need a different shutdown
# approach you can use one of the following variables:
# o ssl-unclean-shutdown:
# This forces an unclean shutdown when the connection is closed, i.e. no
# SSL close notify alert is send or allowed to received. This violates
# the SSL/TLS standard but is needed for some brain-dead browsers. Use
# this when you receive I/O errors because of the standard approach where
# mod_ssl sends the close notify alert.
# o ssl-accurate-shutdown:
# This forces an accurate shutdown when the connection is closed, i.e. a
# SSL close notify alert is send and mod_ssl waits for the close notify
# alert of the client. This is 100% SSL/TLS standard compliant, but in
# practice often causes hanging connections with brain-dead browsers. Use
# this only for browsers where you know that their SSL implementation
# works correctly.
# Notice: Most problems of broken clients are also related to the HTTP
# keep-alive facility, so you usually additionally want to disable
# keep-alive for those clients, too. Use variable "nokeepalive" for this.
# Similarly, one has to force some clients to use HTTP/1.0 to workaround
# their broken HTTP/1.1 implementation. Use variables "downgrade-1.0" and
# "force-response-1.0" for this.
# BrowserMatch "MSIE [2-6]" \
# nokeepalive ssl-unclean-shutdown \
# downgrade-1.0 force-response-1.0
</VirtualHost>
</IfModule>
# vim: syntax=apache ts=4 sw=4 sts=4 sr noet这里面LocationMatch的路径得跟前面一致,重启一下Appche应该就好了。
配置客户端
客户端没啥难弄的,关键是确保path跟服务端设置一致。端口用443,传输层安全用tls。
速度测试
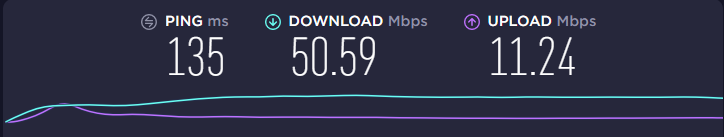
跑了下Speedtest,没开BBR就能跑满我带宽,还不错了。
本文链接:https://blog.stsecurity.moe/archives/99/
This work is licensed under a Creative Commons Attribution-NonCommercial-NoDerivatives 4.0 International License.

